Shipcheck reads your public GitHub repo the way a senior engineer would: looking for the security holes, missing tests, abandoned auth flows, and embarrassing comments your AI coding tool shipped at 2am. Plain English. Specific files. Ranked by what'll actually hurt you.
You vibe-coded a working app in a weekend. The screens look great. The signup flow works on Chrome on your laptop. You are about to push to ProductHunt or send the link to a recruiter or charge a credit card with it. And somewhere in those 4,000 lines is a hardcoded Stripe key, an unsanitized SQL query, a webhook that anyone on the internet can post to, and three TODO comments that say "fix before prod."
The existing audit tools were not built for this. SonarQube wants you to install a daemon, configure Maven, and read a 60-tab dashboard. Snyk speaks a dialect of engineer that assumes you've shipped to production for ten years. GitHub's security tab tells you a transitive dependency from 2019 has a CVE, but does not tell you that you are storing user passwords in plaintext in your Postgres seeds file.
Shipcheck is the audit you wish a senior engineer would do for you over coffee. Plain English. Ranked by what will actually break you on launch day. Specific files, specific lines, with a one-paragraph explanation a non-engineer can act on. Nine dollars a scan, ninety seconds to run, no install required.

Public GitHub repos only for now. We don't ask for OAuth, we don't store your code, we read the public tree.
Static analysis plus a Claude-driven semantic pass that looks for things linters miss: leaked secrets, half-finished auth, fake placeholders.
Ten ranked findings. Each one names the file, the line, the risk in plain English, and the fix in one sentence.
Most findings are 5 to 30 minutes of work. Re-scan free for 24 hours to confirm you closed them.
No "your auth flow could be better." Instead: app/api/auth/login/route.ts · line 42 with one paragraph of plain-English explanation and one sentence of fix. If the finding doesn't tell you exactly what to change, we mark it incomplete and don't charge you.
The stuff that gets you on the front page of Hacker News for the wrong reason.
Not style nitpicks. The stuff that actually breaks when traffic shows up.
What your AI tool forgot to finish before declaring victory.
For technical recruiters reviewing candidate work, the stuff that says "no."

You shipped six apps last quarter, all of them mostly working, none of them audited. You don't read your own code line by line because that is what the AI was for. You need a fast, cheap, honest sanity check before the launch tweet goes live.

Stripe is wired up and you're about to charge a real credit card. You have the mortal fear that you have left a webhook unverified or an admin route unauthenticated. Nine dollars and ninety seconds to know.

You're not a senior engineer. You can't tell whether a portfolio repo is impressive or a one-shot AI copy-paste. Shipcheck gives you a one-page pass-fail with ranked specifics, so you can spend interview time on the candidates whose code earned it.
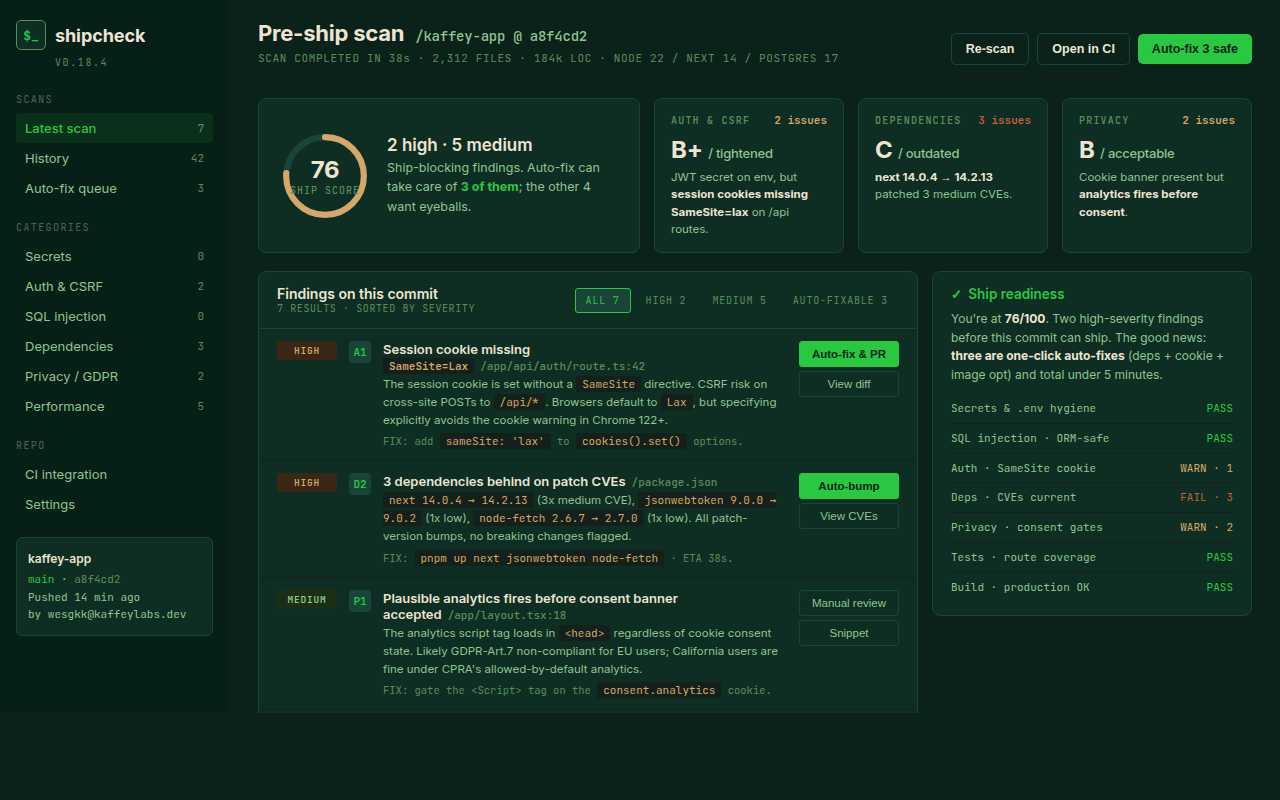
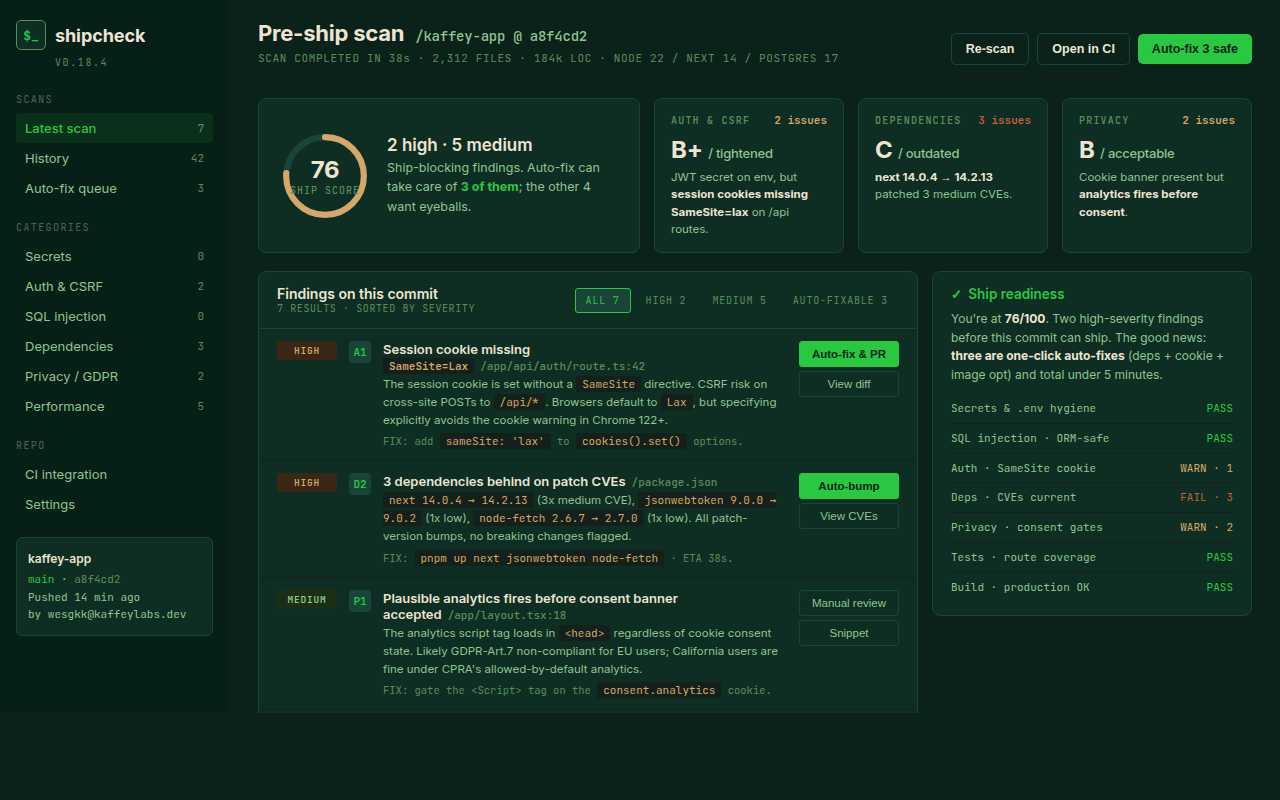
This is what a typical Shipcheck report looks like. Ten findings, ranked, each one in language you can act on without a senior engineer translating.
Your /api/webhooks/stripe route accepts any POST body and trusts it as a real Stripe event. Anyone on the internet can hit it and mark an order as paid. This is the single highest-severity issue in this scan.
The /admin route renders without checking if the visitor is logged in or has admin role. Anyone who guesses the URL sees user list, revenue, and the delete-account button.
Tokens are minted but the expires_at column is never set. A token leaked once is valid forever. Add a 1-hour expiry on token creation and a check on consumption.
The /pricing route renders the literal string "TODO: write feature comparison here." Visitors will see this. Replace before any link goes public.

Most founders run two scans a month, one before launch and one after the first round of fixes. The unlimited plan is for shops shipping a new repo every other week.
Nine dollars. Ninety seconds. Ten ranked findings. Most launches ship with one or two of them open. Don't be most launches.